Last updated: April 6, 2024
Ransomware is malicious software that aims to hold your data hostage in exchange for ransom. To do this, ransomware encrypts your personal data and then the bad guys ask you to pay to get your precious files back.
Modern ransomware models initially appeared in Russia, but we see that the number of attacks of this type has greatly increased in other countries, including Australia, France, and the United States.
In November 2012, McAfee, the publisher of security software, reported having registered 120 new samples of this kind of malware.
How does ransomware work?
Ransomware typically spreads in the same way as a computer worm that loads a malicious program. It enters the system via a file downloaded by mail or a fault in the network. The latter will target file types with sentimental or practical value (photo, video, DOC, PDF, etc.) and encrypt them with a very strong double key (2048-bit RSA).
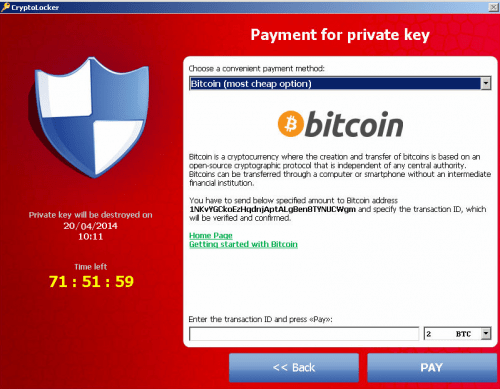
After a few minutes, your most sensitive files become inaccessible and a message appears on your screen. The latter invites you to pay a sum of money to recover the private key used for encryption and thus find your data. Of course the payment method is discreet: Paypal, Bitcoin, etc.
There are in fact other ways of working ransomware. Some will saturate your screen with porn images to make you pay. Users then checkout to avoid being mistaken for perverts.
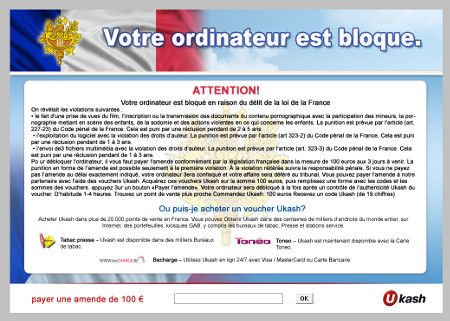
Others will prohibit access to Windows. THE ransomware do not hesitate to pose as the police or a government organization! On the warning window, you will see the logo of your country's police and a message that will explain that a hacker has used your PC to download movies illegally and that you need to pay a fine. Most of the time, people pay for fear of ending up in court.
What to do when your data is held hostage?
Vaccinate your PC
Before any infection you can “vaccinate” your PC with CryptoPrevent, but if it is already too late, disconnect your computer from the Internet, even if it means unplugging the box. You can try disinfection with your antivirus or MalwareBytes.
Know the extent of the damage
To find out the extent of the damage, you can use CryptoLocker ScanTool which will tell you which files have been encrypted. If you are infected, have no backup and all hope seems lost, don't pay the bad hackers!
Victims reported that even after timely payment, the decryption key sent by hackers did not work!
Identify the type of ransomware
Do a research on the Internet because with a little luck your ransomware is not very sophisticated: some actually work with the same encryption key for all victims. You could therefore recover your data with the key of a victim who has already paid! The site Ransomware Decryptor contains private keys seized during police raids on pirates...Why not try?

Carry out disinfection protocols
If you think that all is lost, there are still a few ways to keep hope alive. The site Malware-Tips has an entire section on ransomware and offers disinfection protocols.
If, once disinfected, you had no other choice but to pay the ransom, it happens that certain files are not correctly decrypted (obsolete registry key, etc.). The solution then consists of decrypting them at the same time. hand with crypto-a-locker, a Python script that will detect and decrypt stubborn files.
How can you protect yourself against ransomware?
Make regular backups
We have seen that ransomware targets files that are dear to you (photos, documents, PDFs, etc.). The simplest is therefore to make regular backups on an external hard drive disconnected from the PC in normal times. The free paragon software will do this very well.. For greater comfort, and unless you have a sufficiently large hard drive, you can also make a clone of your system with Macrium Reflect.
Have an updated antivirus
No need to checkout to have resident antivirus protection. Rasomware often attacks with a simple EXE file contained in a ZIP. Free antiviruses like Avira or Avast will quarantine the file as soon as it moves an ear. You will still need to be sure to renew your license and update the viral database.
Pay attention to emails
Be careful when opening attachments to your emails, especially if they are compressed (zipped) and if they contain executable files.





Need help ? Ask your question, FunInformatique will answer you.