Last updated: January 1, 2023
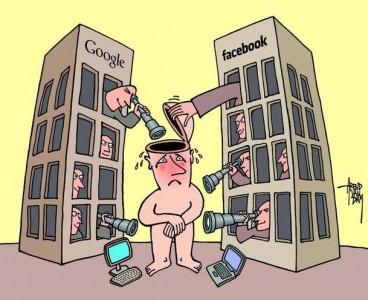
Your online privacy is increasingly at risk. Indeed, large internet companies constantly collect your data for advertising and marketing purposes.
And yes, the information you send over the web is of real gold mines for businesses.
Even if options, settings and tools allow you to more or less protect your private sphere, the simplest and most effective thing is still to adopt good behavior on the Internet. In this article, we give you all the advice for protect your privacy on the internet.
Why protect your privacy on the internet?
It was relatively easy to maintain your privacy before the Internet. At that time, each of us was master of our personal data. Even when you revealed information, it didn't go outside your circle of friends.
Your photos were seen by ten people for the best of them. Your mail was only read by you, only you consulted your address book. You made your purchases almost anonymously and, often, you paid in cash. But that was before.
The internet has changed all that and your private life is now exposed. There is no precise definition of invasion of privacy but it is commonly accepted that the capture and disclosure of information relating to family life, sentimental life, sexual relations, professional life, health , political and religious beliefs.
According to article 9 of the civil code, everyone has the right to respect for their private life. This means that no person, organization or company has the right to collect, use and disclose information about your private life.
In this article, we will see a selection of tools and good methods for protect your privacy on the Internet et surf the web more quietly.
1) Use disposable messaging
Email remains the main activity of Internet users. Many sites and services ask you to register by creating an account. You generally need to provide a nickname, an email address and a password.
The problem is that you are giving your email address to a site that you do not know and that you may not use again.
Instead of providing your real email address, you can provide a disposable address, Yopmail is a website that provides you with a disposable email address for free. Its use is extremely simple. You just have to indicate the address of your choice to yopmail. For example, funinformatique@ yopmail.com and connect to the yopmail.com interface.
For more details I invite you to read this article: create a disposable and anonymous email address.
2) Use encrypted messaging
Internet users exchange a lot of emails and these emails often contain confidential information such as usernames or passwords. Your messages pass through the servers of your email providers. They are not safe listening and spying services and, without being paranoid, they are not immune large data collectors. Your privacy on the internet is therefore exposed.
If you want to keep your correspondence confidential, you can encrypt your messages. You have several solutions for this:
Tutanota: turnkey encrypted messaging
Tutanota, a German-based webmail service that end-to-end encryption of your emails and which incorporates a clever solution to communicate with those who do not use it ...
The entire encryption process is done from home, on your browser. But the best part is that if your correspondent does not use Tutanota, all you have to do is specify a password for your message. The latter must be communicated from a secure method (verbally). With this password, your friend will only have to read your message directly on the Tutanota site.

Mailvelope: use encryption from your webmail
Mailvelope is an extension that gives you the power to use PGP encryption directly from your webmail. The Mailvelope extension, available for Chrome and Firefox browsers, adds a layer of security to Gmail, Outlook.com, Yahoo! Mail and GMX.

Thunderbird + Enigmail
Thunderbird is a messaging and instant messaging client. Libre, distributed free of charge by the Mozilla Foundation.
Enigmail is an encryption extension for Mozilla Thunderbird, it adds OpenPGP message encryption and verification to your email program.
3) Use a web browser that ensures your anonymity
As you know, your Internet service provider may collect data during your web browsing. Indeed, the sites on which you connect also try to collect data. To prevent this, protect your privacy on the Internet by using the Tor web browser.
Tor secures your Internet browsing by routing your connection through multiple servers and encrypting the data you exchange.
Instead of taking a direct path from the sender to the recipient, the data passes between several servers which blurs the lines. Furthermore, Tor allows you to access the network darknet and the hidden service (the invisible web).
For more details, see this article for know how to use Tor.

4) Use a search engine that doesn't spy
Search engines like Google ou Bing use some of your personal data to show you better results and more importantly, to show you targeted advertising.
To avoid this, use a search engine that does not track you and does not collect any personal data. There are two that are very effective and provide good search results: DuckDuckGo et Qwant.

5) use an encrypted chat
To communicate securely with someone, we have seen that it is possible to encrypt your emails. So why not use encrypted instant messaging as well.
We therefore advise you to replace Skype or Facebook Messenger by Tox.
Tox is free software from instant messaging, voice over IP and video conferencing. It does not require any installation, 100% encrypted and allows you to chat in writing, via Video or to send files to each other. For more info, see this article: UTOX: an encrypted and free alternative to Skype.

6) Share files anonymously
If you want to share files securely and anonymously then the best ideal solution is to use OnionShare.
It is an application that you allows file sharing to your relatives and friends anonymously. With OnionShare, you will be able to transfer files in using Tor network. Thus, the surveillance services and other curious little ones will see nothing but fire.

To share a file with OnionShare, follow the steps presented in this article: Onionshare: Share a file anonymously with TOR
7) Encrypt your data before sending it to the cloud
If you are using online storage (Dropbox, Google Drive, Microsoft SkyDrive, or others) to store your documents or family photos, you may know that file names and their contents appear in plain text on the servers of these large companies.
A simple hack and all your data is in danger. We well remember the hacking of nude photos of Jennifer Lawrence and Kirsten Dunst on iCloud.
The solution then consists of encrypt data before sending it to these remote servers. BoxCryptor allows you to encrypt your files automatically and send them to the cloud. I invite you to read this article: encrypt your data before sending it to the cloud.
8) Clear metadata from your photos
You may not know it but your photos contain hidden data, which are not necessarily visible at first glance. This data is of a very diverse nature and provides information on the model of your device, your name, GPS coordinates, the date of the photo taken, etc.

Unfortunately this data may contain sensitive information which should not come out.
We remember very well the member Anonymous who was spotted by the FBI thanks to a photo. He has indeed revealed his place of residence to the FBI by posting a simple photo on a forum.
To remove metadata from your photos, use Geotag Security.
Read this article to learn how to use it.
9) Encrypt the contents of your hard drive
Protecting your private data also means protecting it. make it inaccessible in case of loss or theft. A user account with password is insufficient. The solution is touse encryption.
You can use full disk protection using bitlocker. There is also VeraCrypt a French alternative to TrueCrypt to protect files on the hard disk or the contents of an external hard disk.
Otherwise to make encrypted backups, there is cobian-backup, software that supports AES 256-bit encryption.
10) Use a free and open source operating system
La Gnu / Linux distribution Tails is especially designed to preserve privacy on the internet of those who use it. This is the distro that uses Snowden and quite a few other activists to connect securely.

Tails, contains all the tools you need to be completely anonymous and to protect your privacy on the internet. Among these tools we find:
- Tor to surf the Internet without leaving any traces, as well as its Torbutton in order to protect itself from malicious JavaScript codes.
- HTTPS Everywhere, an extension that forces your browser to access websites only in https mode.
GnuPG, the free version of PGP.
- TrueCrypt, which allows you to encrypt a single file, an entire partition of a hard drive, or a device, such as a USB flash drive.
- PWGen, a strong password generator
- A virtual keyboard in order to protect yourself from keyloggers which record everything you type on your computer keyboard.
- MAT (Metadata Anonymization Toolkit) to anonymize the metadata contained in the files; (creation and modification dates, GPS coordinates, identity of the computer or camera user, etc.).
To know how to install Tails on a USB key, I strongly advise you to read this document.
11) Secure your phone and tablet
Your personal data may be collected and disclosed when you use your smartphone or tablet. Actually, the risk is greater with a smartphone than with a computer because you have fewer tools to defend yourself.
Be aware that installing an antivirus on your phone doesn't mean you're completely secure.
So here are the best apps to stay anonymous. Applications to encrypt your conversations, protect your data, and keep control of your mobile.
Encrypt your phone calls and messages texts
The telecommunications services provided by the companies are not secure and can be spied with relatively inexpensive equipment. This means that your own government, a foreign government, as well as criminals and hackers can listen to your phone calls and read your messages.
Therefore, we recommend that you install thesignal application on your mobile. In fact, the application Signal allows you to encrypt your instant messages.
Browse anonymously with your mobile phone
OrbotProxy is a mobile application which uses the Tor network to make your internet traffic anonymous without ever knowing where it comes from.
Once downloaded and installed, press the Orbot button in the center so that communications can actually pass through the various Tor relays.
To use Orbot on Android, look at this article and on iPhone, look at this one.
Encrypt your phone data Android
The basic rule when you want to protect your data as little as possible is to encrypt it. Indeed, if you lose your phone, it is quite simple to recover the data if it is not encrypted.
Crypt4All Lite uses AES algorithm with 256 bits to encrypt and decrypt your files. You can use it to encrypt files before putting them on online services (Google Drive, Skydrive, Box, Dropbox, Gmail, etc.) or to store sensitive files on your phone so that they are unreadable to them. curious.
Conclusion
Protecting your privacy on the internet is good but it's not enough. Indeed, you are not alone in publishing personal information about yourself, your loved ones and acquaintances also do so. This can be photos, information, statuses, etc.
All these tools will be in vain if those around you are not aware of the issue of confidentiality and continue to publicly distribute texts, photos and/or personal videos on various community networks.
You must therefore ensure that no personal information about you is not published on the Internet.





cool